The Korean Register of Shipping explains cyber threats and OWASP, analyzing a specific Open Web application and its vulnerability on cyber attacks. The Korean Register of Shipping focuses on the analysis of the ‘A5 : 2017 – Broken Access Control.’
Mainly, a cyber threat is any circumstance or event with the potential to adversely impact organizational operations (including mission, functions, image, reputation), organizational assets, individuals, other organizations, or the nation state through unauthorized access to an information system, causing destruction, disclosure, modification of information, and/or denial of service. Cyber threats need to be categorized periodically to update the vulnerabilities of assets, and the potential impact on that asset.
In addition, the Open Web Application Security Project is an open source web application security project, researching web exposure, malicious files and scripts, and security vulnerabilities.
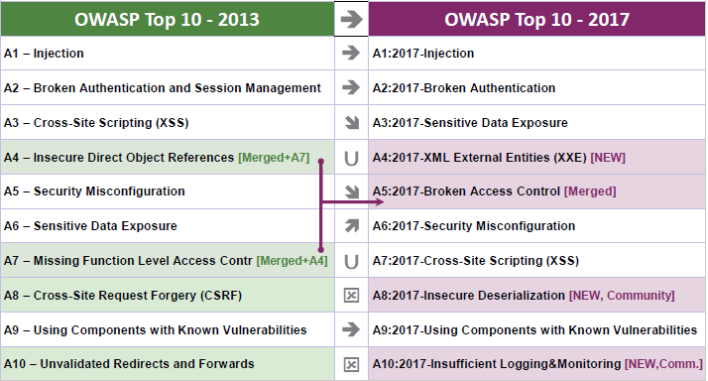
In light of the above, the Korean Register of Shipping focuses on the analysis of the ‘A5 : 2017 – Broken Access Control.’
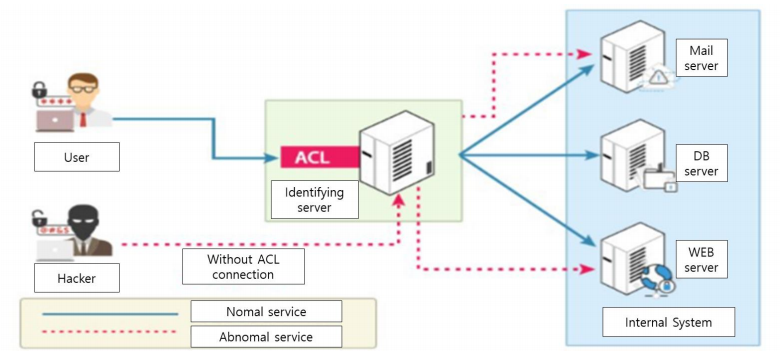
Specifically, the Broken Access Control means that restrictions are not applied properly to what an authenticated user can do. An attacker could exploit this vulnerability to gain access to unauthorized functions, such as accessing a user’s account, viewing critical files, modifying a user’s data, or changing access privileges.
Disabling access control procedures is a key technology required by attackers. There is an application that uses input values in an SQL statement to access user account information without a validation procedure, and an attacker has to access another user’s account if the attacker does not properly validate the input value at the time of transmission from the browser to the server It is possible.