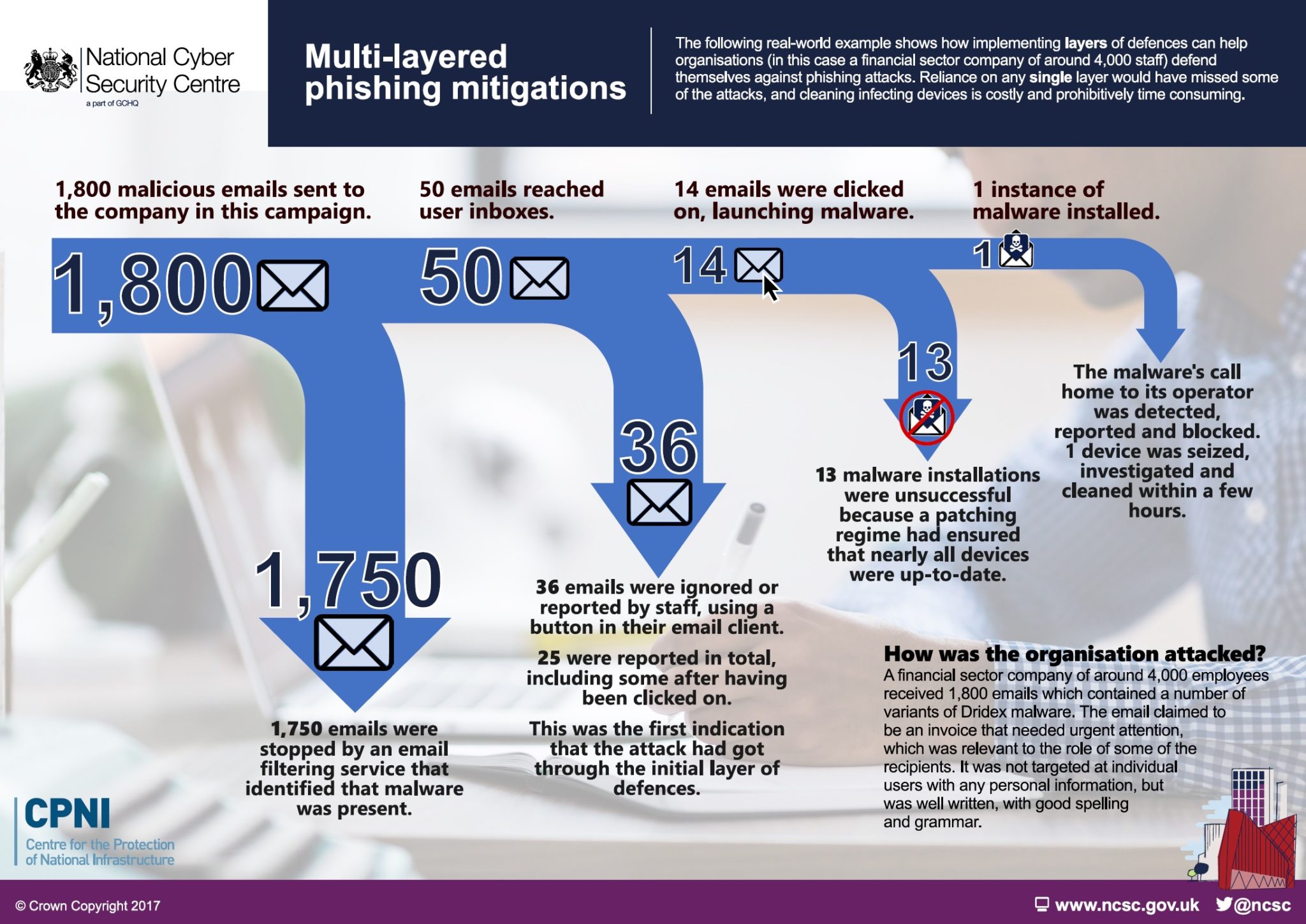
After publishing a multilayered approach model of defense against cyber breaches, the UK National Cyber Security Centre (NCSC) presented a case example of a real attack on a company showing how effective layering of their defences gave them a strong overall defence.
A financial sector company of around 4,000 employees received 1,800 emails which contained a number of variants of Dridex malware. The email claimed to be an invoice that needed urgent attention, which was relevant to the role of some of the recipients. It was not targeted at individual users with any personal information, but was well written, with good spelling and grammar.
- 1,800 emails were sent to the organisation by this campaign
–> 1,750 were stopped by an email filtering service that identified that malware was present.
- This left 50 emails that reached user inboxes.
–> Of these, 36 were either ignored by users, or reported using a button in their email client. 25 were reported in total, including some post click; this was the first indication that the attack had got through the initial layer of defences.
- This left 14 emails that were clicked-on, which launched the malware.
–> 13 instances of the malware failed to launch as intended due to devices being up-to-date.
- 1 instance of malware was installed.
–> The malware’s call home to its operator was detected, reported and blocked.
–> 1 device was seized, investigated and cleaned in a few hours.
Reliance on any single layer would have missed some of the attacks, or in the case of relying on cleaning up quickly afterwards, be very costly and prohibitively time consuming.





























































