New research explores the maritime industry’s relationship with cyber security risks, and makes recommendations to ship owners and operators to improve how those risks are managed within their organisations.
The report “Great Disconnect” was officially launched during a recent webinar, and was produced by maritime cyber security company CyberOwl, maritime innovation agency Thetius and law firm HFW.
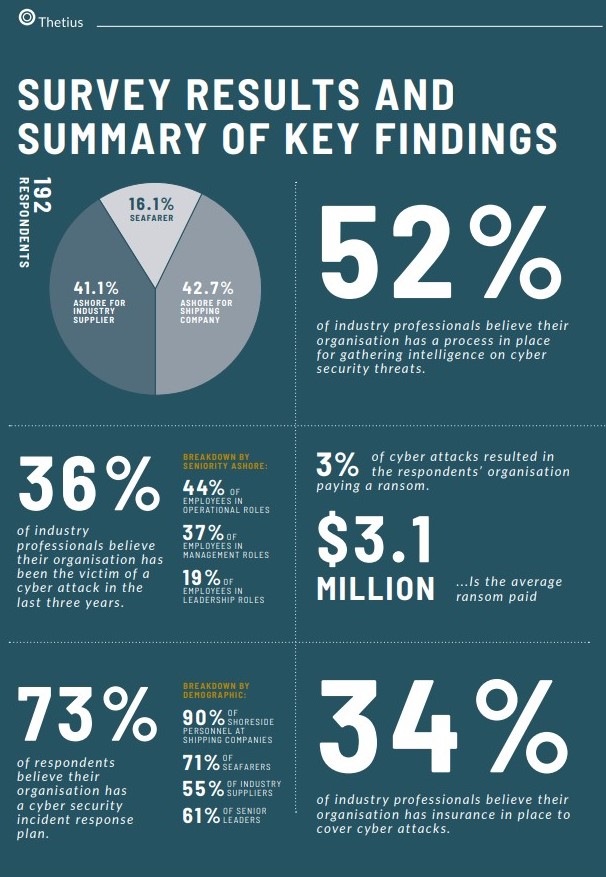
After taking into account the views of more than 200 industry professionals through a combination of an industry survey and research interviews conducted with cyber security experts and stakeholders, the report attempts to shed light on the cyber security readiness of shipping.
However, the authors note that maritime has still a lot to do in order to be better protected from cyber attacks, and for this reason it presented a 4-point plan for the industry to follow in order to enhance its cyber resilience.
Speaking at the webinar, Chris Bhatt, Chief Commercial Officer, Aon explained that “shipping is not taking responsibility, as it passes it all to IT, saying it is their job.” For this reason, he suggests for maritime to spend money to assess vulnerabilities and find potential risk points.
Agreeing with Mr. Bhatt, Ronald Spithout, Industry Expert in Maritime Digitalisation, added that:
As of now shipping has taken half measures regarding cyber security, in order to be compliant. However, these measures are not enough to really protect itself
According to the report, within maritime organisations, there is a disconnect between the perceived and actual readiness to respond to an attack. Whether at sea or ashore, the more senior a member of staff is, the less likely they are to know if their organisation has suffered from a cyber attack.
In fact, at sea, 26% of seafarers do not know what actions are required of them during a cyber security incident, and 32% do not conduct any regular cyber security drills or training. Ashore, 38% of senior leaders either don’t have a cyber security response plan or are unsure if their organisation has one.
Similar issues exist across the maritime supply chain, with a disconnect between the security standards ship operators are working to and the standards that the industry’s suppliers work to
says the report, adding that this problem is compounded by the fact that many operators have little to no control over the security of systems that are installed onboard, creating a disconnect between the exposure for the ship operator and their ability to control the risks.
$3.1 million in ransom
According to the report, 44% of industry professionals reported that their organisation has been the subject of a cyber attack in the last three years, with the key findings of the report noting that:
- 52% of industry professionals believe their organisation has a process in place for gathering intelligence on cyber security threats.
- 36% of industry professionals believe their organisation has been the victim of a cyber attack in the last three years.
- 73% of respondents believe their organisation has a cyber security incident response plan.
- 3% of cyber attacks resulted in the respondents’ organisation paying a ransom.
- $3.1 million is the average ransom paid.
- 34% of industry professionals believe their organisation has insurance in place to cover cyber attacks.
What is more, 83% of shoreside employees at shipping companies agree that they regularly conduct cyber security training and drills in their organisation, but only 67% of seafarers agree.
Additionally, when questioned if their organisation has appropriately addressed cyber risks in the fleet’s safety management system, 87% of seafarers and shoreside employees at shipping companies agreed with this statement.
Recommendations
As the maritime threat landscape is constantly evolving, and the industry needs to remain alert to and learn to adapt to the threat continually, the report suggests certain recommendations in order for shipping to be protected from cyber risks:
#1 Set up dedicated cyber security directorate within fleet operations that covers both IT and OT security: It is critical that the directorate takes overall responsibility for security and is given the authority and resources to be able to gather data-driven evidence of the actual state of cyber security within the fleet assets and operations on which to base its decisions for improvement.
#2 Implement comprehensive cyber incident training and drill programme: The programme should be based on practical scenarios that reflect the actual setup and security posture of the organisation, its people, processes and technology.
#3 Develop minimum security standards for suppliers and partners: This can be designed as a supplier code of connection which sets a minimum cyber security standard for the supplier before they are permitted to connect to vessel systems or access to data from the vessels.
#4 Conduct urgent review of insurance policies and seek specific legal guidance on ransom payments: All vessel operators should conduct an urgent review of insurance policies throughout their organisation to understand any risks that are not fully covered. Operators should also seek legal advice on ransom payments specific to their circumstances and incorporate the findings into their cyber security response plan.