Chris Adams, Head of Loss Prevention, Steamship Mutual, discussed how cyber risks affect navigational safety at the 2017 SAFETY4SEA Conference. Considering that the computerization of operating and control systems on vessels requires effective cyber security arrangements, it is vitally important to raise awareness of cyber security risks with personnel and to implement safe practices to avoid putting systems at risk. If however, navigational data should be compromised by a cyber event, traditional navigation skills should ensure that the ship is not placed at risk. Mr. Adams presented two case studies to question whether there is confidence that shipping assets are really protected.
My flight yesterday was delayed, as there was a fault with the aircraft which made it unsafe to go to Athens. I don’t know about you, but when men with toolboxes appear on an aircraft, I feel distinctly uncomfortable. It turned out to be a computer issue. One of the flight computers was defective, but was easily resolved: they installed a new one and confidence soared. It was only a computer issue, what could possibly go wrong? After all, if a computer fails on a plane, surely we could rely on the pilots to be able to fly the machine.
Computerization and connectivity on ships is increasing all the time. But the level of computer control and automation on ships has not reached the same levels as in the aviation industry. So, if computers on ships become unreliable, how great are the risks?
Cyber security is a very hot topic at the moment and it seems to be constantly on the headlines, we are all aware of it, we all fear the day when we open our computers and see a message on the screen that says “All your files have been encrypted. In order to reinstate those you need to pay a ransom.”
The issues that give rise to those risks are familiar. To counter those risks we build defences. In medieval days, communities defended themselves by building castles. They were extremely difficult to attack and penetrate, but with a bit of lateral thinking, you can get round even the strongest defenses. The legend of the Trojan horse tells us that it is far more effective to work from the inside.
So, in the cyber context, the firewalls, the anti-virus software, are the electronic version of a castle. But if you are to successfully attack, it is easier to manipulate those on the inside to do work for you, using legitimate credentials. That is where social engineering fits in and where we see that the vulnerable human, as always, is the weak link.
It is dramatic to think of a hooded hacker seizing control of a ship somewhere and steering this ship to disaster with the crew powerless to intervene. But this is an over-dramatization. The cyber threat to ships exists at a much more mundane level and it is similar to the threats that exist in any organization ashore.
As human is the weakest link, it is vitally important to raise cyber security awareness, to train with your personnel in cyber security issues and have robust procedures in place.
Conventional wisdom has it that if a ship’s system becomes compromised, you have watchkeepers in place who will note when data becomes unreliable and they will then apply traditional navigational skills to avert disaster. Are we confident about that? Can we sleep easy, knowing that valuable assets represented by the ships, the cargoes they carry, and the personnel onboard, are adequately safeguarded by those to whom we entrust their safe navigation?
The “Rickmers Dubai”, in January 2014, was involved in a collision with a small tug “Kingston” and its tow, which was an unmanned crane barge, called “The Walcon Wizard”. The collision happened in the Dover Strait, and both vessels were in the south westbound traffic lane of the traffic separation scheme.
It was a typical January night in the English Channel. There was a force 5-6 southwesterly wind, the sea state was moderate to rough, but visibility was good. It was the 0.00-4.00 am watch, the Rickmers Dubai was bound from Hamburg to Genoa. She was making a course over the ground of 233°T at 15,4 knots. The officer of the watch was the 2nd officer, experienced and qualified for a number of years, and this was his second trip on the vessel.
The vessel was well-manned and she had onboard a bosun and four ABs and that meant there was an able-bodied seaman (AB) to act as a dedicated look-out.
But at the time of this incident, the AB, who was destined to be in the wheelhouse during this watch was down below carrying out safety rounds.
The vessel was using ECDIS as the primary means of navigation, but she also had an X-band radar with ARPA fitted that was in use.
The Kingston was bound from Ipswich to Southampton, and she was making good a course of 237°T. She was being overtaken by Rickmers Dubai, as she was doing only 6 knots, she had a tow that was 250 metres astern of her and both the tow and the tug were lit. But significantly, the tug was not transmitting information on AIS, she was not of a size that required mandatory fitting of an AIS transmitter.
Due to the absence of this important information; the Channel Navigation Information Service (CNIS), which looks after this particular area of the channel, was issuing a safety broadcast to mariners, at regular intervals, to warn of the presence of tows and it had issued a broadcast at 23.40 and another at 00.40. There was due to be another one, at 01.40, but that was not made because of pressure of other work on the watch manager. There was no evidence that any of those broadcasts were heard by the watchkeeper on the Rickmers Dubai.
In the findings of MAIB, the 2nd Officer was found to be relying entirely on the ECDIS, but because there was no AIS transmission from the tug, the tug was effectively invisible on the ECDIS screen. She was not invisible on the radar, but it is clear that the radar was not used as an aid to an effective look-out.
The inquiry also found there was a low state of arousal of the 2nd officer. He was alone on the bridge and music was heard on the background; a very relaxing atmosphere not consistent with the level of traffic in the environment.
Although it was not causative of the collision -and this is relevant to the issue of cyber security- on the forensic examination of the USB dongle to the VDR, it was found that a movie had been deleted from that, so that piece of equipment had obviously beenused for inappropriate purposes.
The 2nd officer first saw the lights of the tug when it was very close and fine on his port side. On that point the tow was just off the port bow, he did not see the tow. He decided that he was going to alter course to port, in order to pass the tug down its portside, completely unaware that he was overtaking a towing vessel.
The Rickmers Dubai then contacted the crane barge, fouled the tug’s tow line, the lead of that changed rapidly from astern to ahead and the tug was towed backwards at over 14 knots, with its towing deck submerged. Unfortunately, the towing winch hydraulics failed, the brake failed and the line rendered, but it was extremely fortunate that no one was killed.
The second incident involves a bulk carrier, the Victoria that grounded in the Kattegat in September 2015. She did not take a pilot, even though this is a difficult passage. The officer of the watch was the Chief officer. At the time of the incident, 6.15 pm, the ship had a speed of 12.2 knots. The weather conditions were favourable , with moderate sea conditions and moderate wind. She was on manual steering, so the individual who was there to act as a look-out was actually on the wheel, so the ship had no dedicated lookout.
The attention of the Chief Officer was distracted by the fact that he was trying also to supervise the deck crew who were applying sealing foam to the vessel’s hatch covers.
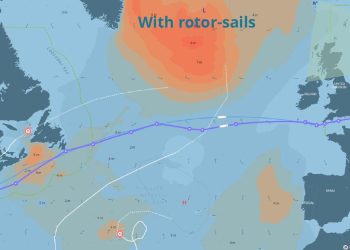
The intended track of the vessel was 340°Tbut in order to achieve that a compass course of 335° had been set to allow for set. But if you look at the AIS records, the ship was actually making good 353° T on average.
Also, during the Chief Officer’s watch, the third officer relieved him for a meal break for about 20 minutes. But despite there being a 2nd watchkeeping officer involved, for a period of almost 2 hours between 4.25-6.15 pm, the ship’s position was not verified, the course steered was not checked, and no navigational marks were sighted.
Apart from being distracted by the crew’s work on deck, the Chief Officer was also fatigued because of the cargo operations at the load port, but the effect of all of this was that the vessel ran aground at over 12 knots on a rocky shoal that was clearly marked on the chart.
What I would like you to do now is to consider some cyber event that occurs to a ship that has the effect of making some AIS information invisible: it introduces a GPS error that puts the ship in a position that is consistently west of its true position. We have seen in the news, relatively recently, an incidence of GPS spoofing in the Black Sea, where GPS signals were incorrect- it is not impossible.
Further, there could be something else that introduces an error between the gyrocompass and the autopilot that actually puts the ship on a track that is 13 degrees east of that which is been set.
Are we confident that a watchkeeper is going to detect those errors?
Both of the above incidents involve identical issues..
You may view his video presentation by clicking here.
The views presented hereabove are only those of the author and not necessarily those of SAFETY4SEA and are for information sharing and discussion purposes only.
[divider]
About Chris Adams, Head of Loss Prevention, Steamship Mutual
 Chris Adams served at sea as a navigating officer with Ellerman City Liners of London. He holds a degree in Nautical Studies from the University of Southampton and joined The Steamship Mutual Underwriting Association Limited as a claims executive in 1979, initially specialising in handling collision and other admiralty incidents. He has been a partner of Steamship Mutual’s management company since 1998 and is Head of the Club’s European Syndicate and Head of Loss Prevention. In the latter role he has conceived and developed the Club’s series of loss prevention DVDs which include programmes on Collision Avoidance, Groundings, Crew Health, Cyber Security, and Piracy; the latter winning the Seatrade Award in the Safety at Sea Category. In addition, in over 20 years of cooperation with Videotel, more than 90 onboard safety training programmes have been jointly produced, the content of which greatly benefit from the Club’s claims experience. He is a Fellow of the Nautical Institute, Younger Brother of Trinity House, Member of the Royal Institute of Navigation, Liveryman of the Worshipful Company of Shipwrights, Freeman of the City of London, a Trustee of the Maritime London Officer Cadet Scholarship Scheme, and Chairman of the International Group’s Pilotage Sub-Committee.
Chris Adams served at sea as a navigating officer with Ellerman City Liners of London. He holds a degree in Nautical Studies from the University of Southampton and joined The Steamship Mutual Underwriting Association Limited as a claims executive in 1979, initially specialising in handling collision and other admiralty incidents. He has been a partner of Steamship Mutual’s management company since 1998 and is Head of the Club’s European Syndicate and Head of Loss Prevention. In the latter role he has conceived and developed the Club’s series of loss prevention DVDs which include programmes on Collision Avoidance, Groundings, Crew Health, Cyber Security, and Piracy; the latter winning the Seatrade Award in the Safety at Sea Category. In addition, in over 20 years of cooperation with Videotel, more than 90 onboard safety training programmes have been jointly produced, the content of which greatly benefit from the Club’s claims experience. He is a Fellow of the Nautical Institute, Younger Brother of Trinity House, Member of the Royal Institute of Navigation, Liveryman of the Worshipful Company of Shipwrights, Freeman of the City of London, a Trustee of the Maritime London Officer Cadet Scholarship Scheme, and Chairman of the International Group’s Pilotage Sub-Committee.




























































Nice abstract from the speech given.
Interesting that VDR USB tongle was used to store movies…
We need to address attitudes in parallel with knowledge when it comes to new technology (…and not only).