In its February 2020 newsletter, the Korean Register introduces wireless networks in relation to their vulnerability and potential countermeasures.
It is said that wireless networks are often replaced with wired cables by many types of wireless network technologies, such as Wi-Fi and Bluetooth, which are widely used in everyday life except cellular communication, as well as Zigbee and Z-Wave, which provide low-power networks with sensors and controls.
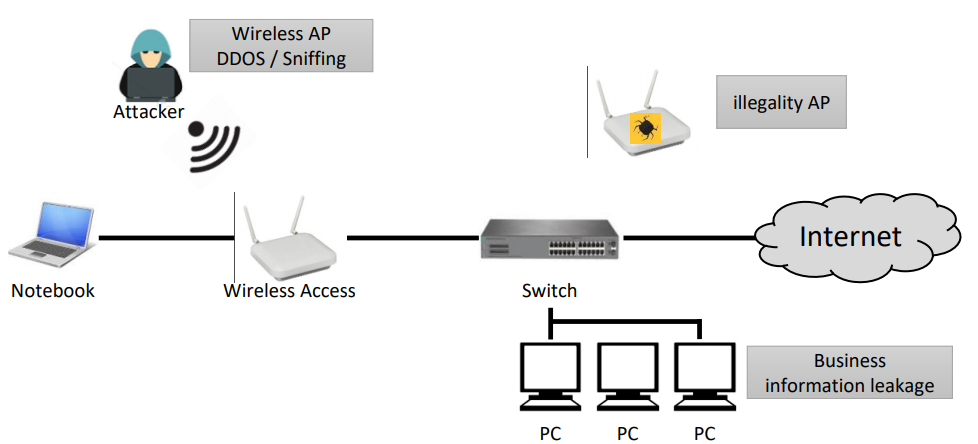
Wireless networks are often used in environments in the existing concept of wired LAN expansion; and most of them are composed of the form of connecting wireless AP to existing wired LANs and installing wireless LAN cards to clients.
Thus, the separation of wired LAN and wireless LAN is not considered at all- KR stresses that this constitutes a security problem.
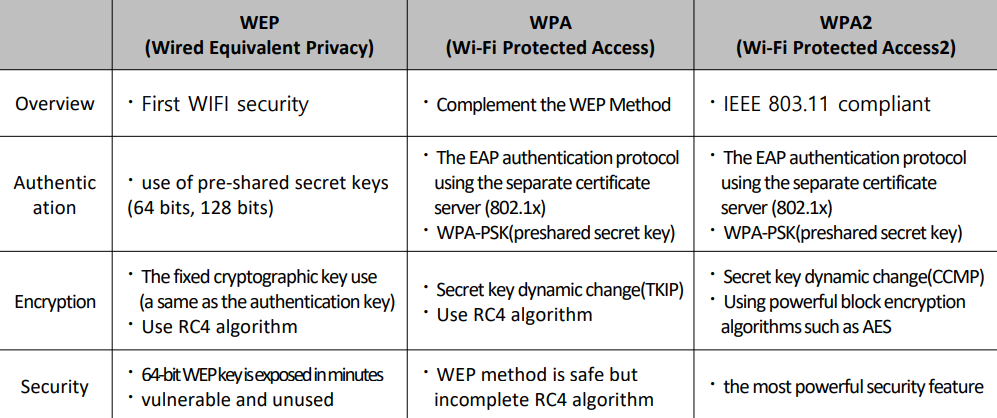
The vulnerability of WLAN can be classified into problem of the authentication during wireless network access and encryption vulnerability of wireless transmission data. In the first WLAN standard, IEEE802.11, the encryption of the wireless LAN authentication and transmission data was not included, but the first WEP method was introduced at IEEE 802.11b, and now WPA and WAP2 methods are widely used.
Previously, the Korean Register of Shipping launched its guidelines for achieving a network security; The guidelines consisted of the explanation of network security, the ways to secure a network and also guidance on cyber security system requirement.
What is more, the KR has suggested that security procedures should be established during remote work and proper identification, authentication, and access control measures should be established when accessing the internal network via the public network, and recovery and management of access rights and equipment should be completed.
In addition, the classification society prompted smartphone users to follow some rules, to ensure their’s and their company’s safety:
- Do not download suspicious applications, do not visit untrusted sites;
- Delete unclear or suspicious messages and messages from senders;
- Use the password setting function and change password on a regular basis;
- Always update operating systems and anti-virus programs to the latest version.































































